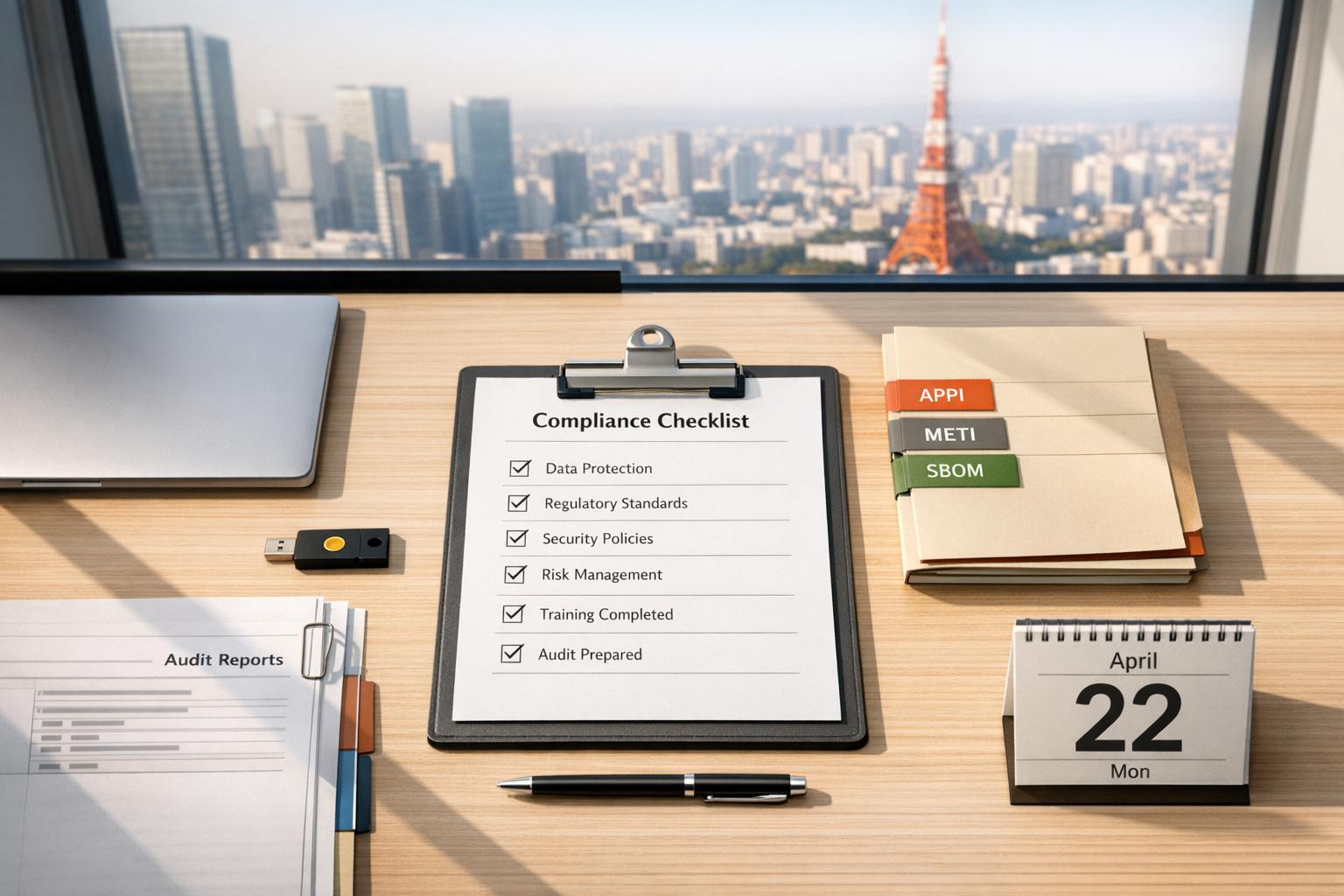
SaaS companies operating in Japan face strict compliance requirements, including data protection under APPI and cybersecurity standards from METI. These regulations impact not only your company but also your local partners like resellers and distributors. This is a common strategy when considering options for Japan entry. Without proper compliance, your SaaS solution risks being rejected by Japanese enterprise buyers.
Key Points to Address:
- APPI Compliance: Covers personal data handling, breach notifications, and cross-border data transfers. Violations can result in fines up to ¥1 billion (~$7–8 million).
- Cybersecurity Standards: METI guidelines emphasize leadership-driven security, supply chain risk management, and certifications like JC-STAR for IoT/SaaS products.
- Training Program Essentials: Include pre-training assessments, localized Japanese-language templates, and role-specific training for partners.
- Ongoing Compliance: Regular audits, risk assessments, and updates to align with evolving regulations.
Staying compliant isn’t just about avoiding penalties – it’s a must to gain trust and do business in Japan’s highly regulated market.
Core Compliance Requirements in Japan
Japan SaaS Compliance Framework: APPI vs METI Guidelines Comparison
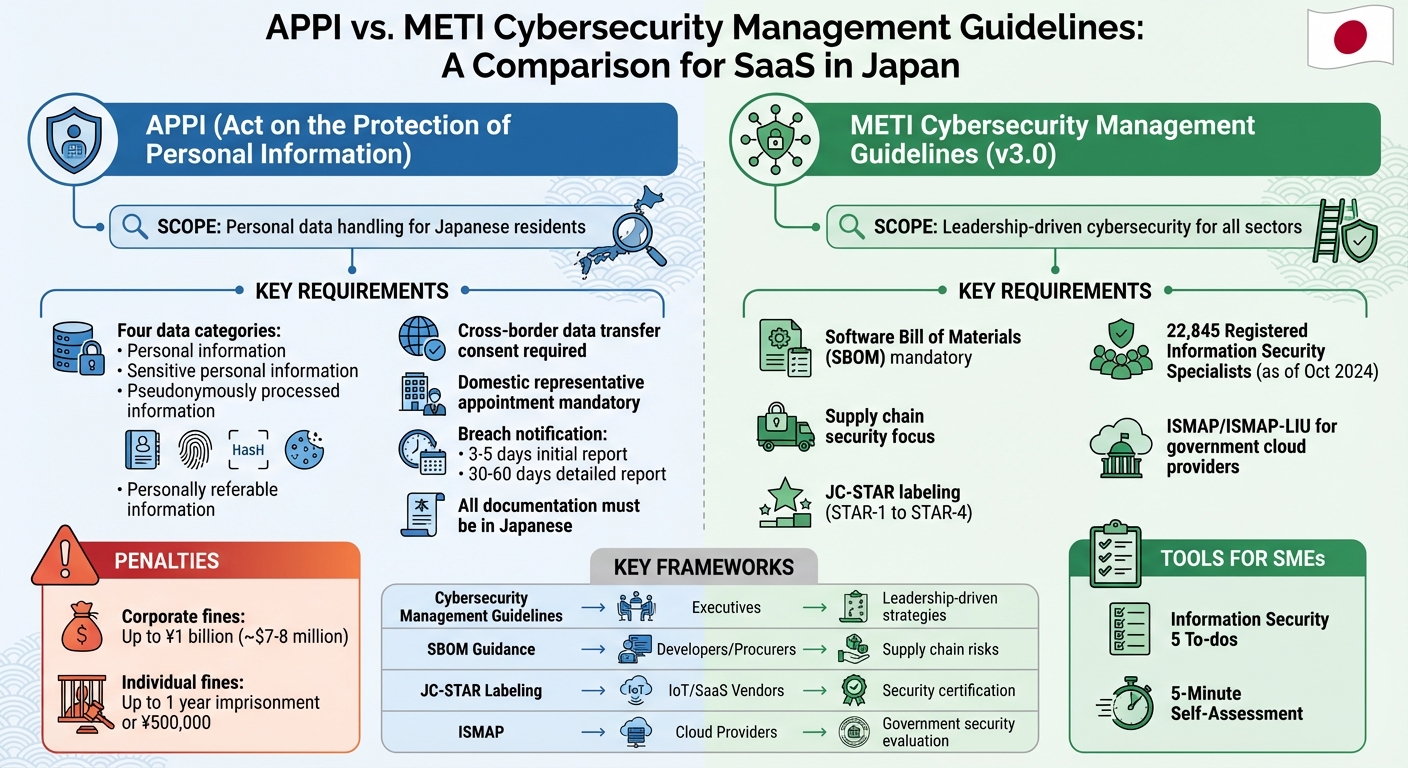
APPI (Act on the Protection of Personal Information)
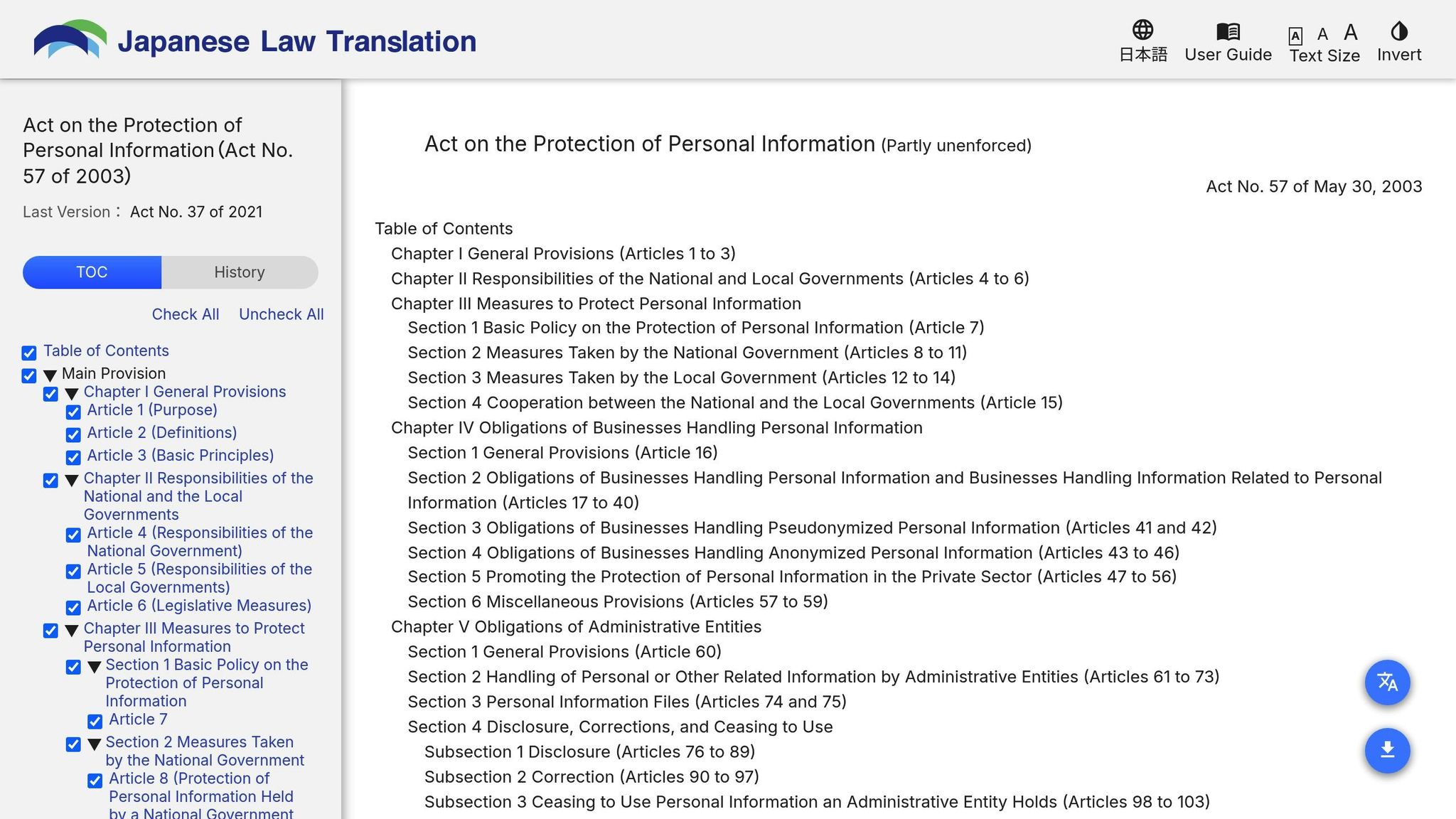
The APPI applies to any organization handling the personal data of Japanese residents, no matter where the organization is based. For global SaaS providers, this means compliance is required even without a physical presence in Japan.
The law categorizes data into four groups, each with specific obligations:
- Personal information: Data that directly identifies individuals, such as passport numbers or biometric details.
- Sensitive personal information: Includes details like race, medical history, or criminal records. Collection or transfer requires explicit opt-in consent.
- Pseudonymously processed information: Data that remains anonymous unless linked with other information, offering more flexibility for internal use.
- Personally referable information: Data like cookies, IP addresses, or device IDs. Transferring this data to third parties who can identify individuals requires consent.
When transferring data across borders, you must secure informed consent, rely on an adequacy decision (currently limited to the EU and UK), or establish contractual safeguards that meet APPI standards. Additionally, individuals have rights to access, correct, delete, or object to the processing of their data. They can also request data portability.
Violations of APPI carry steep penalties. Corporate fines can reach up to 1 billion yen (around $7–8 million), and individuals may face up to one year of imprisonment or fines of 500,000 yen. Breach reporting is mandatory if incidents involve sensitive data, financial harm, malicious intent, or impact over 1,000 people.
Foreign SaaS providers must appoint a domestic representative to handle inquiries from the Personal Information Protection Commission (PPC) and regulatory actions. Importantly, all breach notifications and related documentation must be submitted in Japanese. To prepare, companies should create Japanese-language templates and update service agreements with clauses for immediate breach notification, ensuring alignment with APPI rules.
With APPI covered, the next step is understanding the cybersecurity standards outlined by METI.
METI Cybersecurity Management Guidelines

APPI requirements are complemented by the Ministry of Economy, Trade and Industry (METI) Cybersecurity Management Guidelines (Version 3.0), which apply to organizations of all sizes and sectors, including global SaaS providers and their Japanese partners. These guidelines emphasize cybersecurity as a leadership responsibility rather than just a technical issue.
A major focus is software supply chain security. METI’s "Guidance on Introduction of SBOM for Software Management" mandates a Software Bill of Materials (SBOM) to identify component vulnerabilities and manage licenses.
For smaller partners like local resellers or system integrators, METI offers simplified tools such as the "Information Security 5 To-dos" and the "5-Minute Self-Assessment", which provide practical steps for improving basic security practices. As of October 1, 2024, Japan has 22,845 Registered Information Security Specialists (RISS) under its national qualification system.
For SaaS providers involved with IoT components, the Japan Cyber STAR (JC-STAR) labeling scheme is critical. This voluntary program certifies security standards compliance with four levels (STAR-1 to STAR-4), aligned with international frameworks like NISTIR 8425. STAR-1 certification began in March 2025, and these labels are becoming increasingly important for government procurement.
| Guideline/Framework | Target Audience | Primary Purpose |
|---|---|---|
| Cybersecurity Management Guidelines | Executives (All sectors) | Promote leadership-driven cybersecurity strategies and investments |
| SBOM Guidance (Ver. 2.0) | Software Developers/Procurers | Address software vulnerabilities and supply chain risks |
| Information Security 5 To-dos | SMEs and Partners | Simplify steps for better security practices |
| JC-STAR Labeling Scheme | IoT/SaaS Vendors | Certify compliance with security standards through voluntary labeling |
| ISMAP / ISMAP-LIU | Cloud Service Providers | Conduct security evaluations for providers working with government agencies |
sbb-itb-a752276
Preparing for Partner Compliance Training
Conducting a Pre-Training Assessment
Start by evaluating your partners’ compliance readiness in relation to the outlined regulatory standards. This includes identifying their specific roles under Japanese law – whether they function as a "business operator" (controller) or a processor. This distinction is crucial as it determines their legal responsibilities and reporting obligations.
Use a detailed questionnaire to gather insights on key areas like organizational security measures, HR policies, physical site security, and encryption protocols. Confirm that partners have established proper data residency practices and obtained explicit consent for any cross-border data transfers.
For foreign SaaS partners, check if they’ve appointed a domestic representative to liaise with the Personal Information Protection Commission (PPC), as required by law. Additionally, ensure that their breach notification processes align with the criteria set by the Act on the Protection of Personal Information (APPI).
Here’s a breakdown of critical assessment categories and verification points:
| Assessment Category | Key Verification Items |
|---|---|
| Legal/Regulatory | APPI compliance, ISMAP registration, Domestic representative status |
| Data Handling | Consent management for cookies/tracking, Encryption at rest/transit, Data residency |
| Operational | Incident management policy, BCP/DRP, Sub-processor list |
| Technical | Penetration test results, IAM controls, Multi-factor authentication (MFA) |
Document all third-party sub-processors involved in your partners’ data handling workflows to avoid any blind spots. Also, confirm that audit logs are maintained for at least 90 days to support potential regulatory investigations in the event of a breach.
Identifying Compliance Gaps
After completing the assessment, use a risk matrix to prioritize gaps based on their likelihood and potential impact. Pay special attention to gaps involving sensitive data, such as financial records, medical details, or national identification numbers. These types of data often require mandatory reporting, regardless of how many users are impacted.
Ensure your partners are clear on their roles, especially regarding immediate breach notifications under APPI. Missing Japanese-language templates for APPI notifications should also be addressed, as the PPC only accepts submissions in Japanese. If these templates are not in place, include them as a key focus in your training program.
Another area to watch for is "Shadow IT" – when employees use unauthorized applications. This is a common source of compliance issues in the growing Japanese SaaS market and should be tackled during training.
To further refine your training, apply the PDCA (Plan-Do-Check-Act) cycle and conduct mock audits. These exercises can uncover documentation gaps and identify personnel who may need additional training. By focusing on actual, real-world shortfalls rather than hypothetical risks, you can design a training program that directly addresses the most pressing compliance challenges your partners face.
Building a Compliance Training Program
Structuring Training Around APPI Requirements
To align your training program with APPI compliance, focus on the four main areas: organizational, personnel, physical, and technical controls. Clearly define reporting structures, ensuring that partners acting as data processors report directly to the data controller. Any breaches must be reported immediately by these partners.
For personnel controls, implement measures like non-disclosure agreements, background checks, and regular security awareness training sessions. Physical security training should emphasize compliance with data center location standards and protection of backup storage. On the technical side, training should address best practices such as end-to-end encryption (both at rest and in transit), multi-factor authentication, single sign-on, and strong identity and access management protocols.
"Article 25 requires ‘necessary and appropriate supervision’ over contractors handling personal data. This duty cannot be delegated – you remain responsible for security measures your vendors take." – SecurePrivacy
If your partners work with government agencies or regulated industries like telecom (MIC), financial services (FSA), or healthcare (MHLW), include sector-specific training. These modules should address stricter notification timelines, as some incidents require reporting within hours. Additionally, ensure all training materials, notification templates, and incident reports are in Japanese, highlighting the importance of localization for SaaS products in Japan, as the Personal Information Protection Commission does not accept English-only submissions. These steps are essential for maintaining compliance beyond the initial training phase.
Using Industry Standards and Certifications
Incorporating established industry frameworks can strengthen your training program. Standards like ISO 27001, SOC 2 Type II, and NIST CSF 2.0 provide a reliable basis for demonstrating comprehensive security controls to Japanese regulators and customers. Map these frameworks to APPI requirements, especially for handling sensitive data breaches.
"ISO 27001 and NIST frameworks offer robust guidelines for information security management. Compliance with these standards indicates that a provider implements organizational and technical controls effectively." – Josys
For partners working in the public sector, include training on ISMAP readiness to meet strict governance and technical control audits. Additionally, integrate the Japan Cyber STAR (JC-STAR) framework into your program. Encourage partners to complete the STAR-1 Assessment Checklist as a self-evaluation tool to identify security gaps and achieve recognized security labels in Japan.
By grounding your program in these standards, you’ll establish a strong framework for compliance training. This foundation is a critical component of a successful SaaS GTM in Japan.
Delivering and Tracking Training
Offer detailed onboarding training and require annual refreshers for all employees with access to sensitive data. Customize training modules by role, providing tailored content for technical teams, sales staff, and management to address their specific APPI-related responsibilities.
Leverage automated systems to monitor training completion and manage consent. Maintain thorough documentation of all training activities, as corporate penalties for violating PPC orders can reach up to ¥100,000,000 (roughly $680,000).
Conduct incident response drills every six months to ensure partners can meet APPI’s tight reporting deadlines – initial reports to the Personal Information Protection Commission are required within three to five days, with follow-ups at 30 and 60 days. Regular mock audits are also invaluable for identifying gaps in documentation and flagging individuals who may need additional training before a real incident occurs.
Maintaining Compliance After Training
Setting Up Internal Audits and Reviews
Regular audits are a must to confirm that personal data is being handled in line with what’s been communicated to data subjects. Your audit team should also look into how contractors are supervised, as you’re legally accountable for the security measures your vendors adopt under APPI Article 25.
Ensure that foreign recipients of data are meeting required security standards. These checks should include technical reviews focusing on encryption, access controls, and vulnerability management. Make sure to keep privileged access logs for at least 90 days.
"APPI compliance is not just about avoiding fines; it’s about creating sustainable data protection practices that build trust and ensure secure business operations in Japan’s digital economy." – Thomas Lambert, Senior Data Protection Consultant at PDTN
Additionally, data subject requests – like those for disclosure, correction, or deletion – should be processed within 2–4 weeks. It’s worth noting that financial penalties for severe violations can climb as high as ¥1 billion (around $7–8 million).
These audit practices are essential for managing risks consistently and enabling quick corrective actions when needed.
Creating Risk Assessment and Correction Processes
Building on your earlier assessments and audits, it’s important to have ongoing processes for evaluating risks and addressing issues. Since the APPI is reviewed every three years, staying updated on regulatory changes is crucial. When launching or modifying business operations, conduct Privacy Impact Assessments to identify any potential privacy risks. For organizations serving the public sector, ISMAP’s continuous monitoring may require reassessments if there are major changes to your control environment.
A recent example highlights the importance of this: in March 2024, the PPC rejected a cloud provider’s application due to weak technical controls, emphasizing the need for thorough risk evaluations.
To streamline compliance, appoint a domestic representative in Japan to liaise with the PPC and handle security incidents efficiently. Additionally, set up workflows to notify the ISMAP Steering Committee immediately if there’s an incident with significant user impact.
Record-Keeping and Documentation Requirements
After completing audits and risk assessments, precise record-keeping becomes critical. Maintain detailed consent records for sensitive data and any extended uses. Ensure your data processing agreements clearly define vendor responsibilities, security protocols, and breach notification processes. Document all points where personal information is collected, specifying the purpose for each data category.
Keep a log of data subject requests along with your responses – access requests usually need to be addressed within 30 days. For formal breach notifications and regulatory submissions, ensure all materials are prepared in Japanese. Having pre-made templates for incident reports can save time. For ISMAP or industry-specific audits, retain technical evidence like incident logs and root cause analyses that meet Japanese standards.
| Documentation Category | Essential Records | Retention Period |
|---|---|---|
| Operational Security | Privileged access logs, BCP/DRP documents | Minimum 90 days |
| Incident Response | Incident logs, root cause analyses, PPC notifications | Indefinite |
| Third-Party Risk | Signed DPAs, vendor security assessments, sub-processor lists | Duration of relationship |
| Consent Management | Opt-in records, withdrawal requests, cookie preference logs | Duration of processing |
High-risk data breaches usually need to be reported to the PPC within 72 hours. To simplify compliance, consider using a consent management platform to automate the collection and tracking of user preferences. This can help demonstrate due diligence during audits.
Conclusion and Key Takeaways
Summary of Compliance Steps
To align with APPI and METI requirements, start by conducting pre-training assessments to pinpoint compliance gaps. Develop a four-tier compliance program that addresses organizational, personnel, physical, and technical controls. Don’t forget to include domestic representation requirements in your framework.
Key actions include ensuring partners report breaches to the PPC within 3–5 days, followed by a detailed report within 30 days (or 60 days if malicious intent is suspected). Regular audits should verify encryption protocols, access controls, and vendor oversight. Keep detailed records of consent, data processing agreements, and incident logs. Respond to data subject requests promptly – typically within 2–4 weeks. These measures, combined with concise record-keeping, help mitigate risks. Remember, corporate fines can climb as high as $680,000 (¥100 million), making compliance a financial priority.
By following these steps, businesses can establish a compliance framework that is proactive and ready to adapt.
The Need for Continuous Compliance
Initial compliance efforts are just the beginning. Maintaining compliance requires ongoing vigilance to keep pace with shifting regulations.
"APPI compliance shouldn’t exist as an isolated Japanese privacy program. Organizations comparing Japanese SaaS companies vs. global comps benefit from integrated privacy governance frameworks." – SecurePrivacy
The APPI undergoes review every three years, with amendments made in 2015, 2020, and 2022, and more updates anticipated by 2026. This evolving landscape means compliance isn’t a one-and-done task. Partners need consistent support to monitor changes and adjust their operations. For example, the PPC is increasingly denying the "cloud exception" when technical access controls are lacking, forcing more providers into rigorous audit frameworks.
Cross-border data transfers demand regular monitoring to ensure foreign recipients uphold strong security measures. Staying informed about changes in destination countries’ legal environments is critical. With Japan’s SaaS market expected to hit $13.6 billion (¥2 trillion) by 2027, investing in continuous compliance isn’t just about meeting regulations – it’s about safeguarding your business and staying competitive.
FAQs
Do we need APPI compliance if we don’t have an office in Japan?
Yes, APPI compliance is necessary even if your business doesn’t operate from Japan. The law has an extraterritorial reach, meaning it applies if you handle the personal data of Japanese residents or offer products or services to people in Japan. It’s crucial to align your practices with these requirements to steer clear of any legal complications.
What should our partners do first to pass Japanese enterprise security reviews?
When working with Japanese enterprises, it’s crucial to adhere to the country’s strict data privacy regulations. This means putting robust data protection measures in place and ensuring you have clear, explicit user consent for handling their data. These steps are essential to pass the rigorous security reviews often required by Japanese companies.
How do we handle cross-border data transfers under APPI?
Japan’s Act on the Protection of Personal Information (APPI) sets clear rules for transferring personal data across borders. To comply, transfers must have a legal basis. This could mean sending data to countries that Japan has approved or using contracts that include safeguards similar to those required under APPI.
When relying on consent, individuals must be informed about the data protection standards in the recipient country. Transparency is key – organizations should be ready to disclose transfer agreements if requested. Additionally, safeguards like internal policies or contractual agreements are essential to ensure personal data remains protected throughout the transfer process.